Computers during World War 2 Part 2
Development that is English. Pcs, that have performed an important part within the triumph. To efficiently pay battle, any essential understanding of expected adversary assaults, shifting soldiers, their figures, instruction, guns, etc. Such understanding can be acquired in a variety of methods: enrolling the elderly officials and generals in the headquarters of the Wehrmacht, which possesses proper info to capture the “vocabulary”, intercepting enemy radio communications. Let us simply state, all means are not, although great in its right each one is similarly accessible.
Interception of the command’s cipher was involved in whilst protection providers of additional nations and the Soviet intellect. the log – symbolized the primary issue personally it required since the scenario at the front end transformed quickly lots of periods is undesirable. Below info isn’t present, the log needed to execute in only 1-2 times. But processing devices within the USSR in those days wasn’t.
To secure the key purchases of the Substantial order of the Wehrmacht, the SD, law enforcement, the SS in Nazi-Germany utilized electrical cipher “Enigma”. Actually, prior to the world war that was Next, rods were able to create a precise backup of “Enigma” and delivered it. But without the changing signal, and also the key, that three times each day were transformed, actually getting a getting interceptor the concept to be deciphered by another Enigma it had been difficult.
Electrical cipher device “Enigma”
Important English commanders arranged a key center for fixing the cipher. To produce decryption pcs within this middle constructed A-team of mathematicians, puzzle-lovers, chess people, enthusiasts of numerous regions of understanding as well as two artists. One of the specialists were Turing, who brought 4 of the linguist, and among the teams, which labored for 12 mathematicians. Within the function of some and his team other was to produce a number of pcs that are unique to decrypt communications that are German.
Suggestions and skills of the innovative group Bletchley Park, within the quickest period might be recognized in actual products, among that was an Electro-Mechanical machine “Heath Robinson”, including two photoelectric devices is read in the punched recording in a price of 2 thousand figures per-second (as an endless recording and also the reading mind “Turing machine”), the math device for relays and also the publishing device and machine “PeterRobinson”, “SuperRobinson”, etc., These devices done the theory of attempting various mixtures of the icons of the German signal to get significant communications.
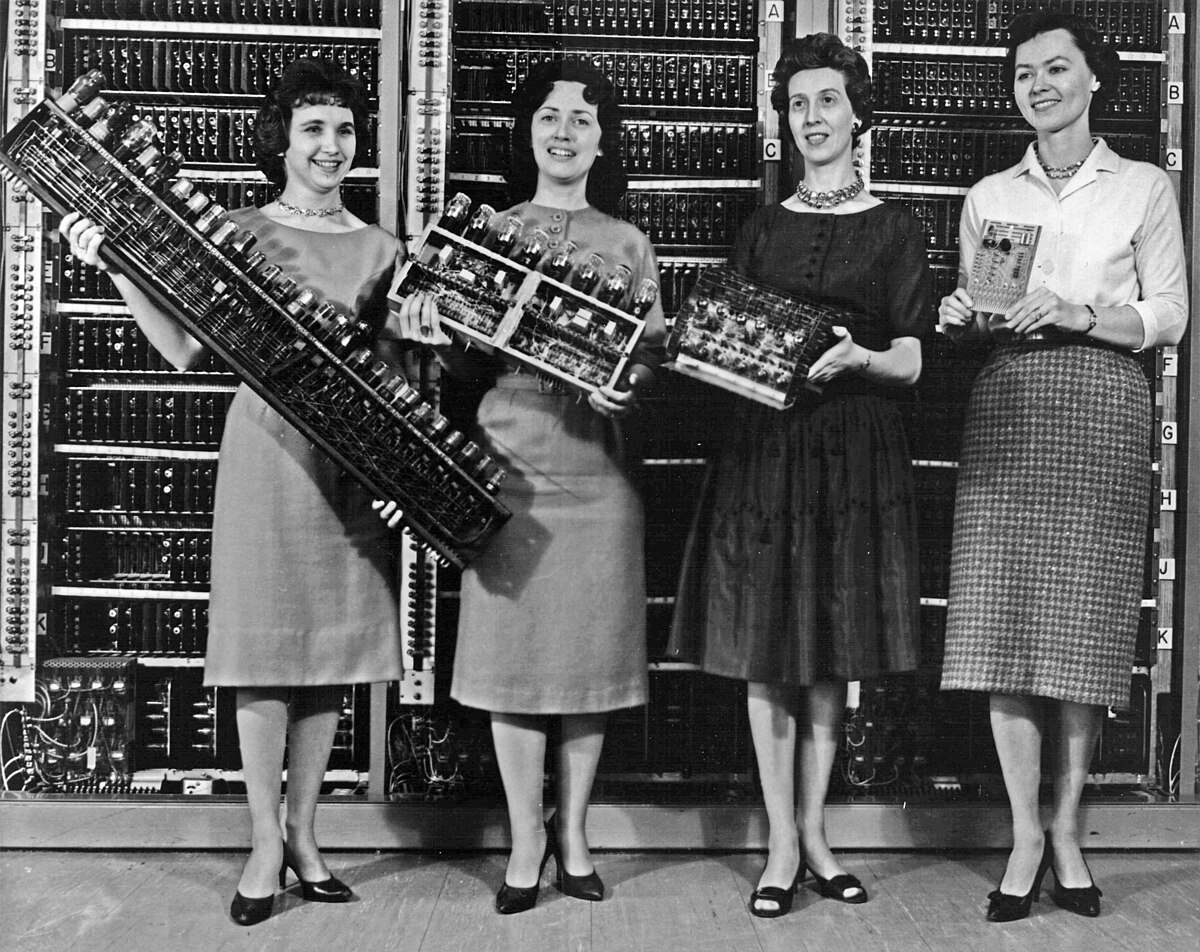
In June 1942 Park came to cryptanalyst and British mathematician Newman, who went the group of specialists. Consequently, in Dec 1943, was made first (not just in England however in the planet) digital processing device Colossus, comprising 2 thousand electron tubes. Even though it is difficult to apply any function Colossus was the very first completely digital processing gadget. Information feedback — your day intercepted adversary communications in a type that was numbered — were completed with recording. The pace that was read was as much as 5 thousand figures per second, it had been employed for 5 products that were select. Device looking for a coordinating compared the protected concept with recognized rules of the Enigma which was saved within the band registers created about the thyratrons. English Colossus pcs (1943) used to decrypt intercepted German communications.
Colossus was the very first PC which performed an important part within the Next world war, and that effectively worked for Matters. From the end-of-the battle was created about 10 of those pcs who labored in the condition Start of Bletchley Park.
“I actually do not wish to state although the battle was gained by us because of the Turing equipment but consider the freedom to express that we’d shed,” remembered over time among the specialists producing Colossus.
Details about the lifestyle of those devices were stored key before the 1970s, Following The battle, Winston-Churchill individually authorized the purchase into components for that damage of the equipment not exceeding how big a human palm. Consequently, due to the elevated secrecy Colossus wasn’t described the background of pcs in several works.
Following the battle…
The best flowering of the usage of Cybernetics for reasons that were military has reached within the postwar time. Pcs are utilized in instruction simulators for that style of the weapons and guided missiles nowadays. The absolute wealthy and most sophisticated countries have previously founded cyber attacks and they’re against nations that were different. Specialists confidently declare that the world-war that is next is likely to be fought in cyberspace. But that is another tale…
